overleaf template galleryLaTeX templates and examples — Recent
Discover LaTeX templates and examples to help with everything from writing a journal article to using a specific LaTeX package.
Template for EAI 320 practical reports
Diese Vorlage dient zur Erstellung von wissenschaftlichen Arbeiten am Lehrstuhl VWL 5 an der Universität Bayreuth. Weitere Hinweise zur Erstellung von wissenschaftlichen Arbeiten befinden sich auf der Homepage des Lehrstuhls.
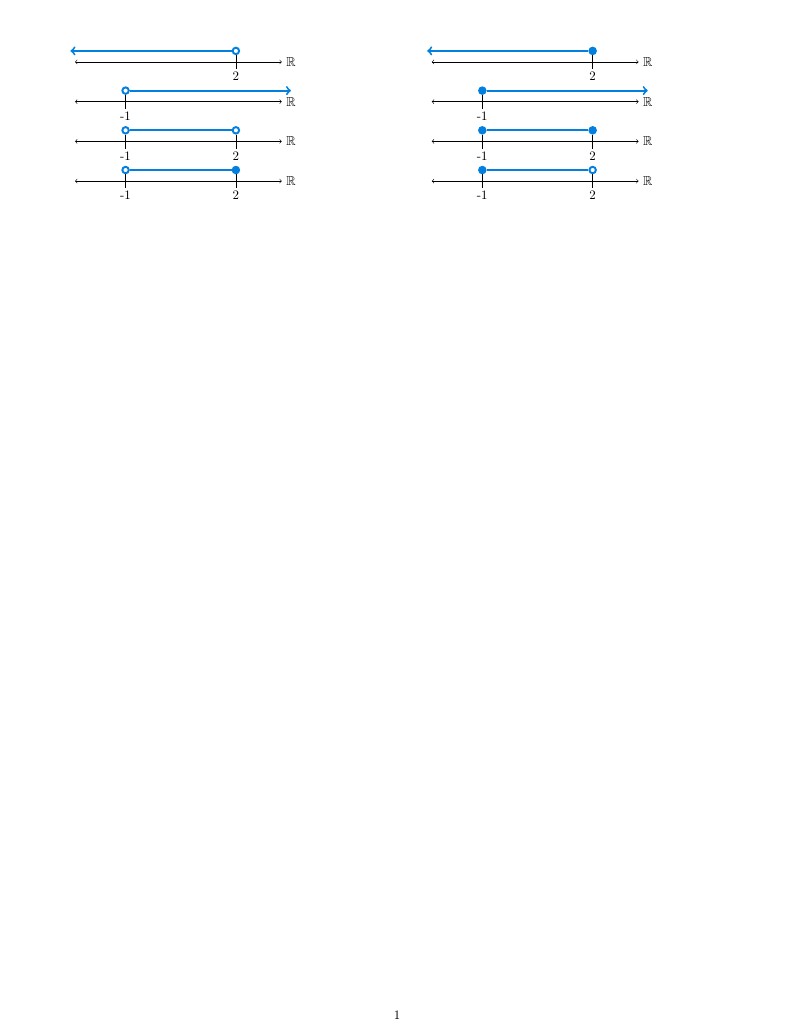
Esta es un ejemplo de cómo utilizar casos condicionales para evaluar las diferentes opciones de un parámetro de entrada en un nuevo macro personalizado, en este ejemplo se condiciona el tipo intervalo que se representa de acuerdo a si se trata de un intervalo infinito o no y si es abierto o cerrado. 2017 por Fausto M. Lagos S. <piratax007@protonmail.ch> Este trabajo puede ser distribuido o modificado bajo los términos y condiciones de la LaTeX Project Public License (LPPL) v1.3C, o cualquier versión posterior. La última versión de esta licencia puede verse en: http://www.latex-project.org/lppl.txt Usted es libre de usarlo, modificarlo o distribuirlo siempre que se respeten los términos de la licencia y se reconozca al autor original
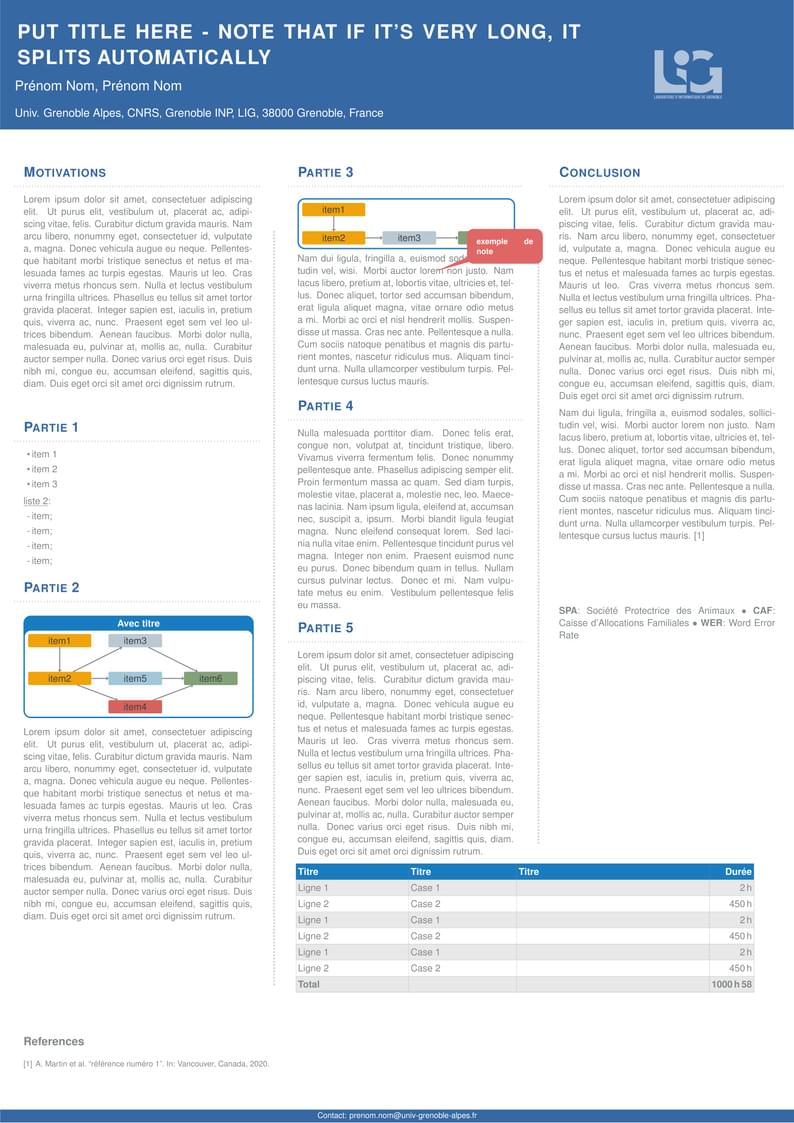
Template de poster pour le LIG, Grenoble
Reporting template for LUT Schools of Business or School of Engineering. Although the main use of this template would be suitable for weekly assignments and/or term papers, with some modifications it could also be used for writing the Bachelor's or Master's Thesis.
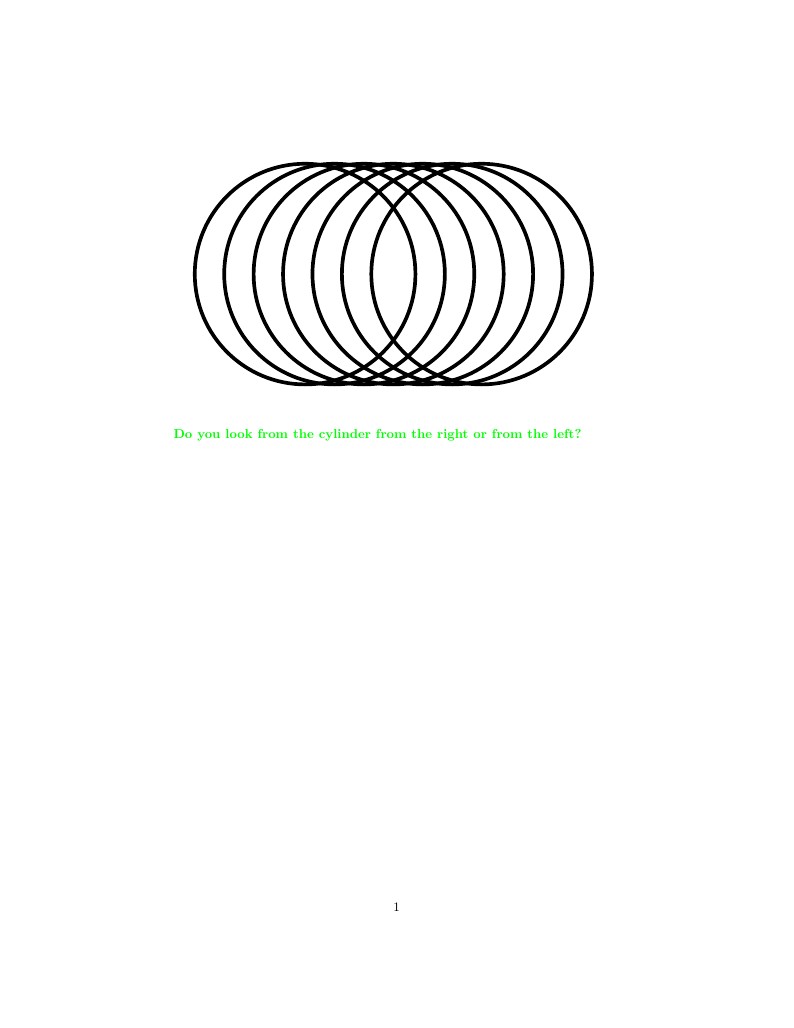
Optical illusion: Do you look from the cylinder from the right or from the left?
山中 卓 (KEK、元大阪大学)が作成された科研費LaTeXを、坂東 慶太 (名古屋学院大学) が了承を得てテンプレート登録しています。 詳細はこちら↓をご確認ください。 http://osksn2.hep.sci.osaka-u.ac.jp/~taku/kakenhiLaTeX/
A high contrast, specialized font template that is designed to be more accessible for a variety of needs. This template uses the IEEE citation style.

This paper presents instructions for preparing papers for the IFMBE Proceedings series. The template is intended to guide the authors in preparing the electronic version of their paper. Only papers prepared according to these instructions will be published in both, the paper and online version of the IFMBE proceedings. In this abstract section you should provide an abstract of your paper, not longer than 300 words.
\begin
Discover why over 25 million people worldwide trust Overleaf with their work.