overleaf template galleryLaTeX templates and examples — Recent
Discover LaTeX templates and examples to help with everything from writing a journal article to using a specific LaTeX package.
Magister
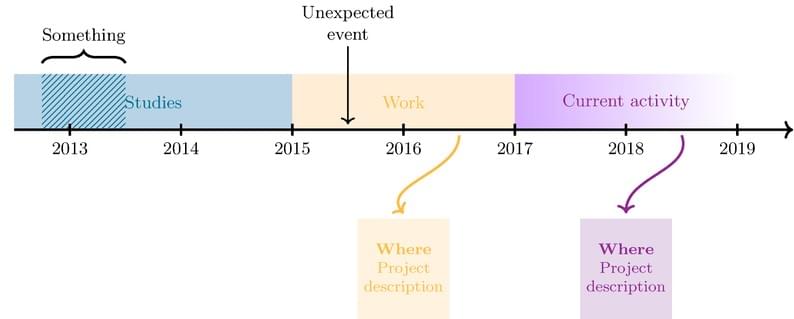
A simple yet colourful timeline
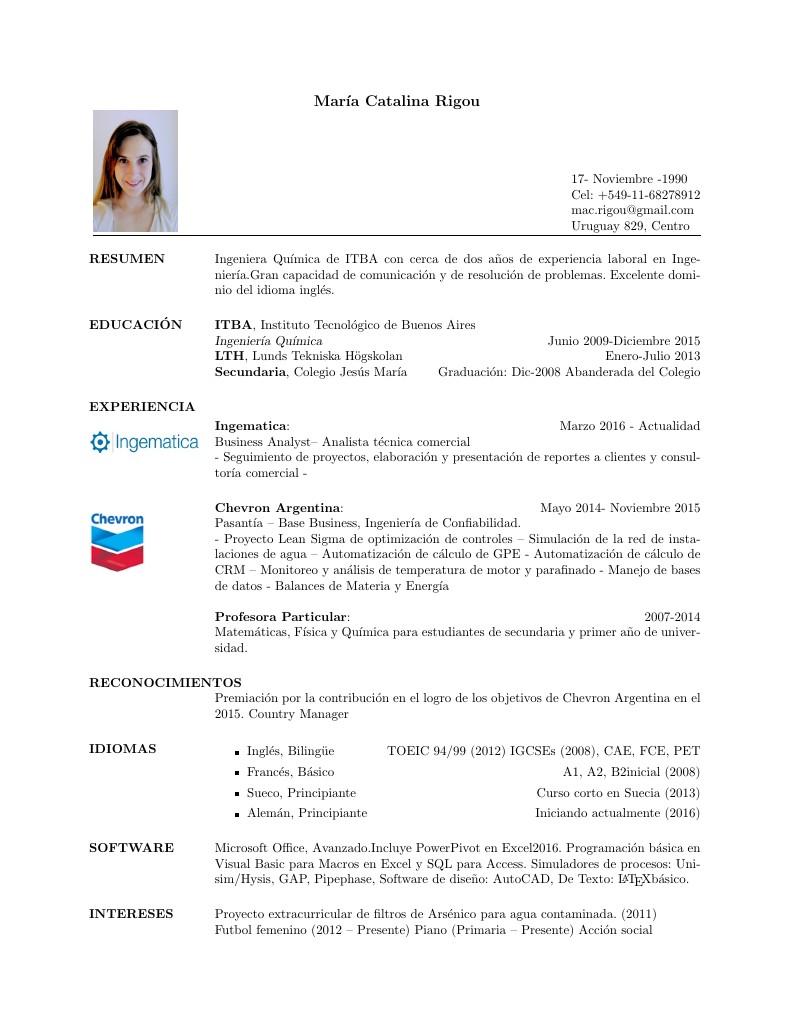
María Catalina Rigou's CV

Title: SOP LaTeX Template Author: Soonho Kong / soonhok@cs.cmu.edu Created: 2012-11-12 http://www.cs.cmu.edu/~soonhok/latex-template-for-statement-of-purpose.html
Template for the bachelor's thesis for the bachelor's degree programme Data Science and Business Analytics at St. Pölten University of Applied Sciences.

Project #1 from Sarah Wright's Calculus I class at Fitchburg State University.

This is a template for the International High Performance Buildings Conference at Purdue, downloaded from the Purdue Conferences website.
Szablon pracy dyplomowej - wydział Automatyki, Elektroniki i Informatyki Politechniki Śląskiej. (Thesis template for the Silesian University of Technology)
一个适用于活泼的中文数学文章的模板.
\begin
Discover why over 25 million people worldwide trust Overleaf with their work.