overleaf template galleryCommunity articles — Recent
Papers, presentations, reports and more, written in LaTeX and published by our community.

Yogesh Patil's CV. Created with the AltaCV template.
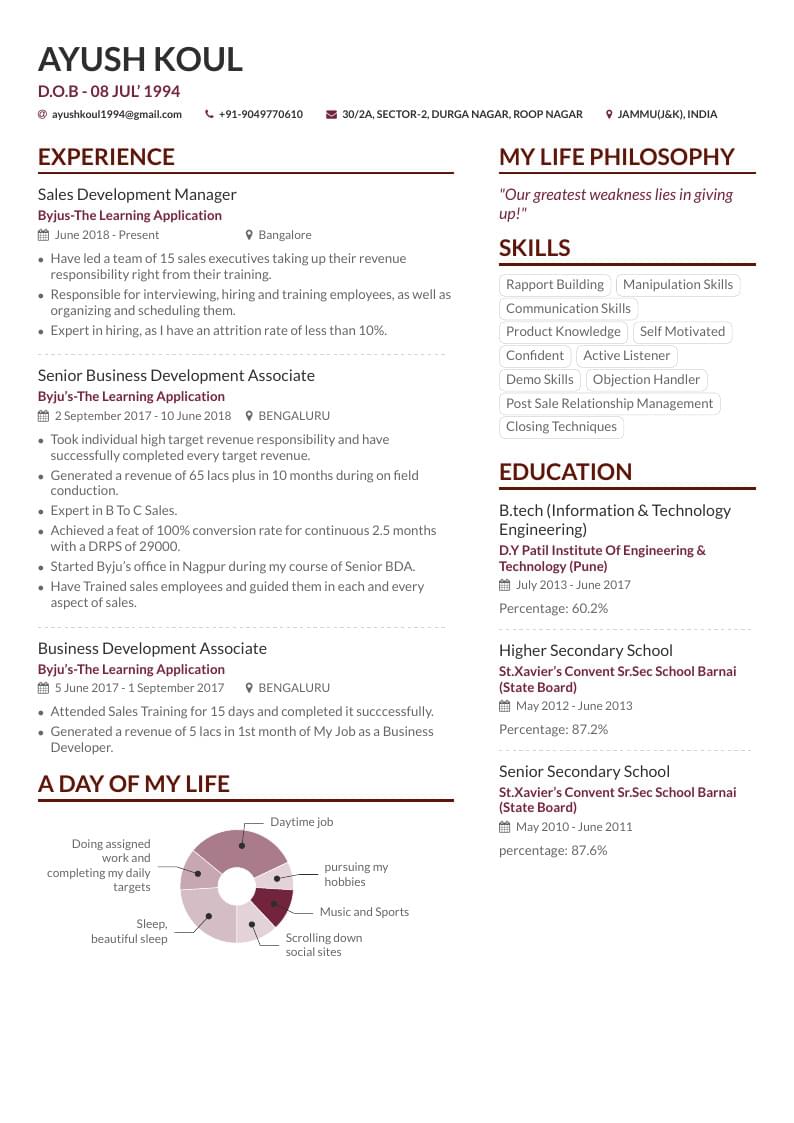
Ayush Koul's CV. Created with the AltaCV template.

Improper oral care is often an unintentional lifestyle that can lead to a variety of health issues. Lacking access to oral health care services is a problem faced by many, which can lead to adverse economic and health consequences. Tooth decay is one of the earliest indicators of inadequate oral health care in children. By utilizing a preventative approach that o ers u- oride tablets to elementary children in uoride-de cient com- munities, the prevalence of oral cavities can be combated.
The main aim of this paper to establish the relations between forward, backward and central finite (divided) differences (that is discrete analog of the derivative) and partial & ordinary high-order derivatives of the polynomials.

En los últimos años se ha visto un auge en el uso de los sistemas de bases de datos NoSQL y junto a ello se ha popularizado la idea de aplicaciones de Persistencia Políglota. Esta consiste en que gracias a la gran variedad y cantidad de datos, y los diversos servicios que pueden dar las aplicaciones hoy en día, es probable que un único tipo de sistema de almacenamiento no sea capaz de cubrir de forma eficiente todas las necesidades de la aplicación. En este articulo se dará una idea general de las Aplicaciones de Persistencia Políglota dando información acerca de su funcionamiento, arquitectura y motivación; y ademas se hablara específicamente de como aplicar la Persistencia Políglota con MongoDB y Neo4j. Palabras Clave: NoSQL, Persistencia Políglota, MongoDB, Neo4j, Neo4j Doc Manager
In Email Analytics, our main focus on criminal and civil investigation from large email dataset. It is very difficult to deal with challenging task for investigator due to large size of email dataset. This paper offer an interactive email analytics various to current and manually intensive technique is used for search evidence from large email dataset. In investigation process, many emails are irrelevant to the investigation so it will force investigator to search carefully through email in order to find relevant emails manually. This process is very costly in terms of money and times. To help to investigation process. We combine Elasticsearch, Logstash and Kibana for data storing, data preprocessing, data visualization and data analytics and displaying results. In this process reduce the number of email which are irrelevant for investigation. It shows the relationship between them and also analyzing the email corpus based on topic relation using text mining.

Thermal wave phenomenon is observed is thin metallic rod by application of periodic heating. In this way, it is demonstrated that there is no wave nature in these improperly called thermal waves by showing that they do not transport energy and its propagation properties can be used to determine the thermal diffusivity of the material.
Deep learning is a fast growing field in tech that is often described to have limitless potential. This paper describes its history, why the explosion in popularity, and how it works. An example of classifying images of handwritten digits (MNIST) will be explored using a fully connected network and a convolutional neural network. Next, a brief description of the tools necessary for the reader to implement his or her own network. Finally, a view of the state of the art being developed by companies such as Google, Facebook, and Baidu.
A presentation to Faculty of Engineering, University of Ghent, approximating the FirW house style. Voor een presentatie aan de Faculteit Ingenieurswetenschappen kan je de template van Harald Devos gebruiken, die een goede benadering is van de officiële FirW-huisstijl. Mits enige aanpassing is deze stijl ook te gebruiken voor andere faculteiten of aan te passen richting algemene UGent-huisstijl. (Downloaded from LaTeX templates en logo's)
\begin
Discover why over 25 million people worldwide trust Overleaf with their work.